A Survey of Operations Research Models and Applications in Homeland Security
←
→
Page content transcription
If your browser does not render page correctly, please read the page content below
informs ®
Vol. 36, No. 6, November–December 2006, pp. 514–529 doi 10.1287/inte.1060.0253
issn 0092-2102 eissn 1526-551X 06 3606 0514 © 2006 INFORMS
A Survey of Operations Research Models and
Applications in Homeland Security
P. Daniel Wright, Matthew J. Liberatore, Robert L. Nydick
Department of Decision and Information Technologies, Villanova University, Villanova, Pennsylvania 19085
{daniel.wright@villanova.edu, matthew.liberatore@villanova.edu, robert.nydick@villanova.edu}
Operations research has had a long and distinguished history of work in emergency preparedness and response,
airline security, transportation of hazardous materials, and threat and vulnerability analysis. Since the attacks
of September 11, 2001 and the formation of the US Department of Homeland Security, these topics have been
gathered under the broad umbrella of homeland security. In addition, other areas of OR applications in home-
land security are evolving, such as border and port security, cyber security, and critical infrastructure protection.
The opportunities for operations researchers to contribute to homeland security remain numerous.
Key words: government: agencies; planning: government, homeland security.
History: This paper was refereed.
S ince September 11, 2001, the term homeland secu-
rity has entered the vernacular of the United States
and of countries around the world. In the US, it is
form it, the government reorganized several agencies
and programs and evaluated its existing security
efforts (National Commission on Terrorist Attacks
defined as “a concerted national effort to prevent terrorist upon the United States 2004). It put several existing
attacks within the United States, reduce America’s vulner- agencies under one domain to unite their efforts to
ability to terrorism, and minimize the damage and recover better protect the country. The department is orga-
from attacks that do occur” (Office of Homeland Secu- nized into five directorates: border and transportation
rity 2002, p. 2). Despite the recency of the term, for security, emergency preparedness and response, sci-
decades the operations research community has been ence and technology, information analysis and infras-
exploring issues that we now classify under home- tructure protection, and management. Each direc-
land security. As far back as 1960, OR researchers torate contains several agencies that were formerly
were working on such issues. At the seventh inter- housed in different departments of the federal gov-
national meeting of the Institute of Management Sci- ernment. For instance, the border and transportation
ences (TIMS), Wood (1961) highlighted US vulnera- security directorate now includes the US Customs
Service, the Transportation Security Administration,
bility and potential responses to nuclear attack. He
and the Animal and Plant Health Inspection Service,
called on the OR community to develop techniques
which were originally the responsibility of the Trea-
and programs to maintain freedom. Since that time,
sury, Justice, and Agriculture Departments, respec-
operations researchers have focused on such top-
tively. For all of its directorates, the Department of
ics as emergency preparedness and response, airline
Homeland Security states its mission as follows:
security, hazardous material transportation, and cyber
We will lead the unified national effort to secure Amer-
security. All of these areas are increasingly important
ica. We will prevent and deter terrorist attacks and protect
to homeland security. While they have done much, against and respond to threats and hazards to the nation. We
operations researchers still have rich opportunities will ensure safe and secure borders, welcome lawful immi-
available. grants and visitors, and promote the free-flow of commerce
The US Department of Homeland Security (DHS), (Department of Homeland Security 2005).
formed in October 2001, has a broad set of responsi- The mission is reinforced by several strategic goals,
bilities that contribute to securing the homeland. To including awareness, prevention, protection, response,
514Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
Interfaces 36(6), pp. 514–529, © 2006 INFORMS 515
recovery, service, and organizational excellence. Both
the mission and the strategic goals of the DHS pro- Countermeasures portfolios
Biological Reduce the probability and consequences
vide exciting opportunities for operations research.
of a biological attack
Chemical Reduce the nation’s vulnerability to chemical
attacks
Literature Framework Radiological and nuclear Develop and deploy techniques for detection
Many research agendas contribute directly or indi- of radiological materials
High explosives Provide the concepts, technologies, systems
rectly to homeland security. Organizing the litera- analysis, and procedures to interdict
ture concerning homeland security is challenging. terrorists’ use of explosives
Research in homeland security falls under the sci- Component-support portfolios
ence and technology directorate, which is the pri- Border and transportation Prevent the entry of terrorists while ensuring
mary research-and-development arm of the DHS. It security efficient flow of traffic and commerce
Critical infrastructure Develop tools to anticipate, identify, and
describes three main research areas that contribute to protection assess the risks in the nation’s critical
the state of the art in homeland security: (1) coun- infrastructure
termeasures portfolios, (2) component-support portfo- Cyber security Research, develop, test, and evaluate
activities for improving cyber security
lios, and (3) cross-cutting portfolios. The science and Emergency preparedness Plan for, prevent, respond to, and recover
technology directorate conducts and funds research in and response from natural and man-made disasters and
all of these portfolios. A few authors have reported on terrorism
Threat analysis Evaluate extensive and diverse threat
the impact of science and technology, including infor- information
mation technology, on terrorism response (Branscomb
and Klausner 2003, Hennessy et al. 2003). Table 1: The countermeasures and component-support portfolios of the
Department of Homeland Security research portfolios protect against
The main purpose of the countermeasures port-
weapons of mass destruction and support department components,
folio is to protect the US from weapons of mass respectively (adapted from www.dhs.gov).
destruction. Research in this area concerns vulnerabil-
ities and risks surrounding biological, chemical, radi-
ological, and nuclear weapons, and high explosives. In addition, they offer the greatest opportunity for
The research invites collaboration between operations contributions combining OR and homeland security
researchers and physical scientists. (Table 1).
The component-support portfolios focus on increas- We sought articles on OR and homeland security
ing the capabilities of DHS components and help- throughout the world published in academic journals.
ing them to secure the homeland. The components While some military research concerns homeland
include border and transportation security, critical security, it does not fall under the US Department of
infrastructure protection, cyber security, emergency Homeland Security and its research agenda. Jaiswal
preparedness and response, threat and vulnerability (1997) reviewed military OR models and techniques,
testing and assessment, the US Coast Guard, and the and Miser (1998), Bonder (2002), and Hughes (2002)
US Secret Service. In this portfolio, OR has the great- discussed the historical impact of OR on the military.
est history and perhaps the most potential to improve Operations researchers have contributed in many
homeland security. ways to homeland security. We use the DHS science
The cross-cutting portfolios focus on other vulner- and technology framework to discuss previous work.
abilities and risks that extend across the countermea-
sures and component support portfolios. They include
emerging threats, rapid prototyping, standards, and Countermeasures Portfolios
university programs. Although OR could contribute Countermeasure efforts address the risks of biolog-
to cross-cutting, most previous work is better catego- ical, chemical, radiological, and nuclear weapons,
rized in the other two portfolios. and high explosives. The OR community has studied
We focus on the first two portfolios because most problems in this area with notable results. Sullivan
OR-related research has fallen in those portfolios. and Perry (2004) developed a useful framework forWright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security 516 Interfaces 36(6), pp. 514–529, © 2006 INFORMS categorizing terrorist groups’ development of chem- Border and Transportation Security ical, biological, radiological, and nuclear weapons. Border and transportation security problems have They investigated three classification approaches, in- been and continue to be of great interest to opera- cluding a heuristic pattern-recognition method, clas- tions researchers particularly because these types of sification trees, and discriminant analysis. problems are a good match for OR techniques. Within Dyer et al. (1998) and Butler et al. (2005) addressed the DHS framework, border security includes improv- the problem of disposing of weapons-grade pluto- ing the security of the nation’s borders to prevent the nium. Dyer et al. (1998) used multiple attribute utility entry of terrorists, criminals, and illegal aliens while theory (MAUT) to develop a hierarchy of objectives, maintaining the safe flow of commerce and travelers. to evaluate 13 alternatives, and to conduct sensitiv- Transportation security includes the safety of airlines, ity analyses. Butler et al. (2005) used MAUT to help railroads, ships, and trucks. the US and Russia to evaluate alternatives for dispos- ing of stockpiles of weapons-grade plutonium. They Border Security recommended converting the plutonium for use as Papers on border security are just beginning to appear. fuel in nuclear power plants. Munera et al. (1997) Wein and Baveja (2005) studied two programs: the US described the safety and security concerns posed by visitor program and the immigrant-status-indicator- transporting highly enriched uranium used in nuclear technology program. These two programs aim to re- reactors. They used stochastic dominance to evaluate duce visa fraud and detect the entry of watch-listed the risks of road and air alternatives. criminals and suspected terrorists into the United Hupert et al. (2002) used discrete-event simulation States. Using a game-theoretic model, the authors to determine staffing levels for entry, triage, medi- show that the quality of fingerprint images is impor- cal evaluation, and drug dispensing in a hypothetical tant to detection probability and thus system perform- distribution center under conditions of low, medium, ance. They discussed fingerprint-scanning strategies and high bioterrorism attack. Craft et al. (2005) cre- that help counter terrorists’ attempts to minimize ated a series of differential equations to determine the detection. potential number of deaths from an aerosol bioterror attack. Their method included an atmospheric-release Airline Security model, a spatial array of biosensors, a dose-response After the hijacking of commercial airlines that led to model, a disease-progression model, and an antibi- the catastrophic events of September 11th, 2001, the otics model with a queue. Kaplan et al. (2002, 2003) US Federal Aviation Administration and Transporta- also used differential equations to study response to tion Security Administration tightened security mea- a smallpox attack. Walden and Kaplan (2004) used a sures at airports around the country. Barnett (2004) Bayesian approach to estimate the size and time of described a dynamic computer system that uses prob- an anthrax attack to determine the number of persons ability models and data-mining techniques to clas- who might require medical care. Wein et al. (2003) also sify airline-passenger threats. However, many airline modeled emergency response to an anthrax attack. security issues still need attention (Turney et al. 2004). Jenkins (2000) used integer programming to iden- Coincidentally many OR researchers addressed air- tify a small subset of oil spills that are similar to all line security before 2001, focusing primarily on scan- potential categories of spills to predict the type of pol- ning passengers or baggage. Gilliam (1979) employed lutant a terrorist group might use. Buckeridge et al. queuing theory for passenger screening. Kobza and (2005) classified bioterrorism outbreak algorithms and Jacobson (1997) discussed the design of access secu- found that spatial and other covariate information can rity systems in airports. They developed performance improve measures for detecting and evaluating out- measures based on the probabilities of false alarms breaks. Stuart and Wilkening (2005) used first- and and false clears that determine the effectiveness of second-order catastrophic decay models to study the single-device and multiple-device security systems. impact of degradation of biological-weapons agents Jacobson et al. (2000) developed a sampling procedure leaked into the environment. that estimates false-alarm and false-clear probabilities.
Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
Interfaces 36(6), pp. 514–529, © 2006 INFORMS 517
Kobza and Jacobson (1996) studied security-system identified US ports as vulnerable and as very attrac-
design by addressing the dependence between the tive targets for terrorists. Lewis et al. (2003) for-
responses of security devices in multiple-device sys- mulated a shortest-path model for container-security
tems. These articles could help managers to improve operations at US seaports. They identified and ana-
decisions on airport security systems and are some- lyzed trade-offs between the number of containers
what generalizable to other types of security systems. inspected and the costs of delayed vessel departures.
Jacobson et al. (2001) described aviation security as The US railway system must be protected to pre-
a knapsack problem and proposed a model that deter- vent the sabotage of passenger or cargo trains and to
mines how to minimize the false-alarm rate of a given prevent terrorists’ gaining control of hazardous ship-
security system. Barnett et al. (2001) conducted an ments. Glickman and Rosenfield (1984) formulated
experiment to evaluate the costs of bag-match strate- models to evaluate the risks associated with train
gies to the airlines and to the passengers in terms of derailments and the release of hazardous materials,
monetary cost and passenger delay. Jacobson et al. issues that could become important in the event of a
(2003) discussed three important performance mea- terrorist attack.
sures of baggage screening: the number of passen-
Truck Security
gers on flights with unscanned bags, the number of
The main issue for the trucking system is the trans-
flight segments with unscanned bags, and the total
portation of hazardous materials. Many of the arti-
number of unscanned bags. Using examples based on
cles in the OR literature on transporting hazardous
real data, they showed how a greedy algorithm can
materials do not focus on homeland security, that is,
minimize the performance measures. Jacobson et al.
preventing terrorists from hijacking these materials
(2005) discussed the optimization of the first two mea-
and using them in weapons. The literature focuses
sures through the allocation and utilization of screen-
on two related issues: routing vehicles and analyzing
ing devices.
risk. Routing hazardous vehicles involves determin-
The cost of airline security concerns airports and
ing what paths vehicles should take to minimize pop-
commercial airlines. Candalino et al. (2004) discussed
ulation exposure in the event of an accident. Many
a software system for screening checked baggage that
authors have developed algorithms and heuristics for
uses data on purchase and operating costs to allocate
solving various cases of the routing problem (Batta
security devices around the country. They proposed
and Chiu 1986, 1988; Berman et al. 2000; Beroggi
an alternative cost function that includes indirect
and Wallace 1994, 2005; Erkut and Ingolfsson 2000;
costs related to scanning errors. Virta et al. (2003) con-
Giannikos 1998; Jin et al. 1996; Karkazis and Boffey
sidered the direct and indirect costs of scanning poli-
1995; Lindner-Dutton et al. 1991; List and Turnquist
cies based on the passengers selected by the screening
1998; van Steen 1987; Zografos and Androutsopoulos
software.
2004). Related to the routing problem are methods
Long customer waits are an important issue for air-
for treating and analyzing risk (Erkut and Ingolfsson
ports who want to keep passengers happy and reduce
2005, Erkut and Verter 1998, Gopalan et al. 1990, Kara
congestion. Leone and Liu (2003) developed a sim-
et al. 2003, Raj and Pritchard 2000).
ulation model that investigates passenger traffic and
throughput rates for scanning devices. They discov-
ered that the machines’ throughput rates were far Critical Infrastructure Protection
lower than their advertised scan rates. To protect the critical infrastructure, analysts develop
As policies and scanning technologies change, oper- tools to anticipate, identify, and assess the risks in the
ations researchers should find further opportunities nation’s critical infrastructure and attempt to reduce
in airline security. the risks and the consequences of an attack. Potential
infrastructure targets include agriculture and food,
Port and Rail Security banking and finance, dams, high-profile events, infor-
Currently, little operations research deals with the mation systems, public health, national monuments,
security of ports and railroads. Harrald et al. (2004) nuclear power plants, and water systems.Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
518 Interfaces 36(6), pp. 514–529, © 2006 INFORMS
Apostolakis and Lemon (2005) used MAUT to pri- a chemical plant failure and showed that they could
oritize the vulnerabilities in an infrastructure that they greatly improve risk assessment.
modeled using interconnected diagraphs and applied Chowdhury et al. (1999) used linear programming
graph theory to identify candidate scenarios. Brown to limit the availability of confidential information
et al. (2004) applied simulation to study the impacts of in a database while providing access to those who
disruptions and used risk analysis to assess infrastruc- need it. They developed two transportation flow algo-
ture interdependencies. Their purpose was to iden- rithms that are computationally efficient and insight-
tify infrastructure risks and ways to reduce them. ful. Muralidhar et al. (1999) developed a model
Baskerville and Portougal (2003) developed a possibil- to explain how to use data-perturbation methods
ity model that suggests that, during an optimal length to protect information from unwanted access while
of time, the possibility of attack on information sys- allowing maximum access to genuine inquiries and
tem infrastructures is very low. maintaining the relationships between attributes.
The risk associated with major utilities, such as
water systems, is important to homeland security Emergency Preparedness and Response
(Grigg 2003). Zografos et al. (1998) developed a data- Emergency preparedness and response include such
management module, a vehicle-monitoring and com- topics as planning for, preventing, responding to,
munications module, and a modeling module and and recovering from natural disasters and terrorism.
applied them to an emergency-repair operation for Larson (2004, 2006) reviewed the literature on police,
an electric utility company. They used a combined fire, and emergency medical services, and provided
optimization and simulation approach to minimize some coverage of hazardous materials, bioterrorism,
service unavailability. Salmeron et al. (2004) devel- and private-sector response to emergencies. The liter-
oped a max-min model to help determine weaknesses ature can be categorized into (1) early work, (2) loca-
in the electric grid to prepare for terrorist attacks. tion and resource allocation, (3) evacuation models,
Through decomposition, they solved the problem and (4) disaster planning and response.
with a heuristic on two test systems.
Early Work
Green and Kolesar (2004) described a number of
Cyber Security papers on emergency-response systems. Much of the
Research in cyber security helps prevent, protect OR work on managing emergency services originated
against, detect, respond to, and recover from large- with the New York City–Rand Institute. Its work with
scale cyber attacks on the information infrastructure. the New York City Fire Department included a sim-
Although many studies concern network security, few ulation model of firefighting operations (Carter and
can be considered operations research. Krings and Ignall 1970); queuing models of fire company avail-
Azadmanesh (2005) developed a model for trans- ability (Carter et al. 1972); the “square root law”
forming security and survivability applications so for the location of fire companies based on response
that they can be solved with graph and schedul- distance, with a response time-distance function to
ing algorithms. Chen et al. (2005) explained how predict response time (developed by Kolesar and
shared networks and the Internet have focused inter- Blum 1973 and applied by Rider 1976); an empiri-
est on IT security, particularly intrusion detection. cal Bayes approach to alarm forecasting (Carter and
They used data-mining methods (artificial neural Rolph 1974); a stochastically-based integer linear pro-
networks and support vector machine) to identify gramming model and a heuristic algorithm for fire
potential intrusions. Abouzakhar and Manson (2002) company relocation (Kolesar and Walker 1974); a set
addressed network security using two intelligent covering approach for locating two types of lad-
fuzzy agents to respond to denial-of-service attacks. der fire trucks (Walker 1974); heuristics for identi-
Shindo et al. (2000) generated fault-tree and event-tree fying high-priority alarm boxes (Ignall et al. 1975);
structures between a computer-network access point Markovian decision models of initial dispatch of fire
and a process plant. They applied their analysis to companies (Ignall et al. 1982, Swersey 1982); and aWright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security Interfaces 36(6), pp. 514–529, © 2006 INFORMS 519 book pulling together the accumulated work on fire Eaton et al. (1985) applied the MCLP model in deployment analysis (Walker et al. 1979) under sup- Austin, Texas when EMS officials sought to improve port from the US Department of Housing and Urban operating efficiency. Saccomanno and Allen (1988) Development (HUD). used a modified MCLP algorithm to locate emer- The New York City–Rand Institute’s work with the gency response capability for potential spills of dan- New York Police Department included work on de- gerous goods on a road network. Belardo et al. (1984b) ployment related to the 911 emergency telephone sys- extended the MCLP to locate oil-spill-response equip- tem (Larson 1972, 2002); scheduling patrol cars using ment on Long Island Sound. Chung (1986) described queuing and linear programming (Kolesar et al. 1975); other applications of the MCLP. and the patrol car allocation model (PCAM) based Hogan and ReVelle (1986) modified set covering on queuing and linear programming (Chaiken and models to maximize the percentage of the population Dormont 1978a, b). The multicar dispatch queuing that receives backup coverage. Pirkul and Schilling model (Green 1984) was later incorporated into a (1988) developed a backup coverage model for facil- revised version of PCAM (Green and Kolesar 1989) ities with limited workloads or capacities. Batta and and applied to the proposed mergers of police and Mannur (1990) extended the set covering models fire departments in several cities (Chelst 1988, 1990). to include some demand points requiring responses Chaiken and Larson (1972) reviewed methods for from multiple units (for example, fire trucks or ambu- allocating emergency units (vehicles). Chaiken (1978) lances). described six models (including PCAM) developed Church et al. (1991) formulated a bicritera max- with HUD support for fire and police operations and imal covering location model that maximizes the the challenges of implementing them. demand covered within the maximal distance and Location and Resource Allocation also minimizes the distance traveled from the uncov- The early literature on locating emergency service ered demand to the nearest facility. Schilling et al. facilities is based on the location set covering prob- (1979) developed the tandem equipment allocation lem (LSCP) formulated by Toregas et al. (1971). In model (TEAM) and the facility location, equip- this problem, a population is served or covered when ment, and emplacement technique (FLEET) model a facility is located within an acceptable service dis- to allocate equipment with varying capabilities and tance. The objective is to minimize the number of demands. The FLEET model has been effectively facilities while covering all demand points. Walker applied to locate fire stations and allocate equipment. (1974) applied the LSCP to the location of ladder With some modifications, Tavakoli and Lightner trucks in the boroughs of New York City. Plane and (2004) applied Bianchi and Church’s (1988) multi- Hendrick (1977) applied the LSCP to the location of ple coverage, one-unit FLEET model (MOFLEET) fire companies in Denver, Colorado. Daskin and Stern to Cumberland County, North Carolina’s emergency (1981) extended the LSCP to address multiple cover- medical services (EMS) system. age of demand nodes. Current and O’Kelly (1992) applied covering mod- The maximal covering location problem (MCLP) els to locate emergency warning sirens in a mid- developed by Church and ReVelle (1974) relaxes the western city. Building on covering-model research, LSCP’s requirement that all demand nodes are cov- Akella et al. (2005) addressed the problem of locating ered. The MCLP seeks to maximize the total pop- cellular base stations and allocating channels, while ulation served within a maximum service distance, explicitly considering emergency coverage of areas given a fixed number of facilities. Because Church known for vehicle crashes and sites prone to potential and ReVelle leave some population uncovered, they enemy attacks. The Lagrangean heuristic performed include mandatory closeness constraints in their for- very well on test problems and in rural Erie County, mulation. The MCLP is related to the p-median prob- New York. lem (Hakimi 1964), which seeks to locate p facilities Several authors have developed optimization mod- to minimize total demand-weighted travel distances els that include stochastic elements. Daskin (1983) between demands and facilities. developed the maximal expected coverage location
Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security 520 Interfaces 36(6), pp. 514–529, © 2006 INFORMS model (MECLM), which seeks to locate emergency in the ambulance deployment method CALL (com- vehicles to maximize the expected coverage area, puterized ambulance location logic), which located even when multiple vehicles are in use. Batta et al. ambulances to minimize mean response time. CALL (1989) offered an extended version of MECLM. They was successfully applied in central Los Angeles to assumed that the probability that a randomly cho- locate firehouses and in Melbourne, Australia to sen vehicle is busy is independent of any other vehi- plan an emergency ambulance system. Later CALL cle in use. ReVelle and Hogan (1989) proposed a was combined with a contiguous zone search rou- variation of MECLM called the maximum availabil- tine (CZSR) that uses an existing database on inter- ity location model (MALM) in which each constraint zone travel times to locate ambulances in Austin, guarantees that the probability that a demand point Texas (Fitzsimmons and Srikar 1982). Swoveland et al. receives service within an acceptable time is no less (1973) used simulation coupled with optimization to than a required value. In these latter two models, the locate ambulances in Vancouver, Canada. analysts estimated probabilities that vehicles are busy in advance. Ball and Lin (1993) developed a model Evacuation Models similar to MALM except that they directly model Researchers have developed optimization, queuing, the source of the randomness. Goldberg and Paz and simulation models to plan emergency evacua- (1991) developed an optimization model that seeks to tions of buildings and areas. Most of such work relies maximize the expected number of emergency callers on queuing or simulation, although some uses opti- reached within a specified time. mization. Chalmet et al. (1982) applied transshipment Analytical queuing models have been used to eval- and dynamic network optimization models to plan- uate the performance of emergency service systems. ning the evacuation of large buildings. They applied In his hypercube model (1974, 1975, 2001), Larson the models to the evacuation of 322 people from an characterizes the operation of an emergency service 11-story building with four elevators and two stair- system as a multiserver queuing system in which wells and compared the results with an observed the states correspond to all combinations of servers evacuation to reveal possible improvements. busy and idle. This model provides a set of output Smith and Towsley (1981) applied analytical queu- measures, such as vehicle utilization and average ing network models to evacuating buildings using travel time, and has been used to deploy ambu- several examples. They modeled the buildings as hier- lances and police cars in various cities (Brandeau and archical queuing networks. Talebi and Smith (1985) Larson 1986, Larson and Rich 1987). Extensions in- modeled the evacuation of a hospital as a finite closed clude improving the accuracy of the model’s output queuing network model using mean-value analy- measures by allowing the service rates to be server sis. Bakuli and Smith (1991, 1996; Smith 1991) used dependent (Halpern 1977), estimating the probability state-dependent queuing networks that incorporate distribution of travel times (Chelst and Jarvis 1979), a mean-value-analysis algorithm and unconstrained and allowing the dispatch of multiple units (Chelst optimization to solve problems in which the widths and Barlach 1981). Researchers have suggested that of circulation paths in buildings can vary. these queuing models can be used as subroutines Analysts have developed micro-, macro-, and in optimization heuristics (Berman and Larson 1982, mesosimulation models for planning evacuations. Benveniste 1985, and Berman et al. 1987). Carter et al. Micro-simulations track the detailed movements of (1972), Hall (1972), and Chelst (1981) developed other individual entities (cars, trucks, or people) on the analytic approaches. road network. Pidd et al. (1996) and de Silva and Savas (1969) used simulation analysis to evalu- Eglese (2000) describe their development of a spa- ate proposed changes to the number and location of tial decision-support system (SDSS) for contingency ambulances in New York. Fitzsimmons (1973) com- planning in emergency evacuations using a micro- bined queuing and simulation to estimate the prob- simulation model linked to a geographical informa- abilities of particular ambulances being busy. This tion system (GIS). Mould (2001) used discrete-event approach was combined with a pattern search routine simulation to plan the emergency evacuation of an
Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
Interfaces 36(6), pp. 514–529, © 2006 INFORMS 521
offshore oil installation. He considered environmen- of considering the stochastic and time-varying nature
tal conditions, such as wind speed and wave height, of travel conditions in emergency situations, Miller-
while using a prespecified routine for evacuation and Hooks and Mahmassani (1998) developed and tested
assessed the use of helicopters alone or in conjunc- two algorithms for determining the shortest path
tion with fast rescue craft. He applied the model to a under such conditions. Several authors have modeled
fictitious incident using randomly generated weather the problem of transporting vital first-aid commodi-
data. Jha et al. (2004) developed a micro-simulation ties and emergency personnel to disaster-affected
model to evaluate five scenarios for evacuation plan- areas. Haghani and Oh (1996) used a deterministic
ning at Los Alamos National Laboratory. Helbing multicommodity, multimodal network flow model to
et al. (2005) developed simulation models of pedes- plan disaster relief. Barbarosoglu and Arda (2004)
trian flows and used the results of these models as extended this approach to include random arc capac-
well as experiments to recommend designs to increase ity, supply, and demand. They formulated the prob-
the efficiency and safety of facilities and egress routes. lem as a two-stage stochastic program and used
Using behavioral information, Stern and Sinuany- data from the August 1999 earthquake in Marmara,
Stern (1989) used micro-simulation to plan evacuation Turkey.
under a radiological event. Srinivasa and Wilhelm (1997) and Wilhelm and
Macro-simulations do not track individual entities Srinivasa (1997) developed a model that prescribes
but use equations based on analogies with fluid an effective response to an oil spill, which requires
flows in networks (Sheffi et al. 1982). Southworth
such decisions as which components to dispatch, how
and Chin (1987) used macro-simulation to study the
many, and when. They formulated the problem as a
evacuation of a population threatened by flooding
general integer program, using graph theory to gener-
from a failed dam based on empirical data from urban
ate response systems (components and their locations)
and rural areas. A compromise approach is to use
needed by the model. They applied their approach
meso-simulators that usually track the movement of
to actual data representing the Galveston Bay area.
groups of entities.
They applied a heuristic (Wilhelm and Srinivasa 1997)
Disaster Planning and Response and an exact procedure based on strong cutting-plane
How individuals and organizations respond to dis- methods (Srinivasa and Wilhelm 1997).
asters is important in preparing for emergencies. A few researchers have modeled human behav-
Belardo et al. (1984a) discussed response problems ior in emergency situations. Reer (1994) developed
faced by four organizations: the American Red Cross, a probabilistic procedure to analyze human reliabil-
the US Coast Guard, the Regional Emergency Medi- ity in emergency situations using time windows and
cal Organization in Albany, New York, and the New organizational input data. Reer used the loss of main
York State Office of Disaster Preparedness. Averett feedwater at a pressurized water reactor plant as an
(2005) discussed four examples of responding to and example to investigate several organizational alter-
preparing for disasters using various modeling tools: natives. Doheny and Fraser (1996) developed a soft-
(1) discrete optimization and simulation models for ware tool that can be used to model human decision
locating and configuring vaccination centers and redi- making during emergency situations. Their model
recting the flow of patients, (2) a graphics tool for includes frames to represent a person’s characteris-
visualization and collaboration, (3) simulation for dis- tics and perception of the environment, and scripts to
aster management training, and (4) game theory to define typical behaviors for particular situations. They
anticipate terrorist attacks and defend against them. used their model to simulate an offshore emergency
Kananen et al. (1990) extended standard input-output scenario.
models and used multiobjective linear programming
to evaluate the potential impact of emergencies or dis-
asters on the Finnish economy. Threat Analysis
Routing emergency vehicles is important in re- Threat analysis develops the capabilities to evaluate
sponding to emergencies. Recognizing the importance and disseminate extensive information about threatsWright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
522 Interfaces 36(6), pp. 514–529, © 2006 INFORMS
and to identify planned attacks. The US government and Horowitz (2004) modeled counterterrorism intel-
obtains extensive information on threats daily, and ligence using a two-player hierarchical holographic
threat analysis research attempts to detect and doc- modeling game. Kaplan et al. (2005) introduced a
ument terrorists’ intentions. Raghu et al. (2005) dis- terror-stock model that estimates the size of terrorist
cussed a collaborative decision-making framework groups and how that size changes when the terrorists
for homeland security and a connectionist modeling themselves are attacked.
approach that fuses disparate information from sev-
eral sources.
Popp et al. (2004) approached threat analysis from
Discussion and Future Research
an information technology (IT) perspective. They Operations research has contributed to issues related
argued that improved IT can reduce the time needed to homeland security in the United States even
for searching for data, harvesting data, preprocessing before 2001, when homeland security was defined.
data, and turning the results into reports and briefs. We adopted the research framework used by the
They discussed three core IT areas in depth: collabo- US Department of Homeland Security’s science and
ration and decision tools, foreign-language tools, and technology directorate to classify the literature. As a
pattern-analysis tools. These areas offer operations result, we have not included some topics, such as the
researchers opportunities to work in conjunction with military that in some cases could be considered home-
information technologists to reduce terrorist attacks land security.
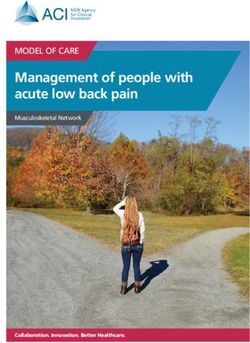
and their effects. We used a two-dimensional framework in exam-
Wang et al. (2004) developed an algorithm that ining the previous OR work in homeland security:
looks for similarities in criminal identities. Using real the areas specified by the US Department of Home-
data from a police department, they created a model land Security and the four phases in the disaster life
that develops disagreement values for each pair of cycle: planning, prevention, response, and recovery
criminal records. The intent is to use IT to determine (Table 2). Planning is generally strategic and long
whether two criminal records represent the same per- term in nature and relates to preparing for a disas-
son. Sheth et al. (2005) devised a process of semantic ter. Planning examples include policy analysis, risk
association that links disparate information to estab- analysis, systems design, and resource allocation. Pre-
lish relationships between terrorists. They incorpo- vention efforts aim to identify and eliminate threats,
rated this methodology into a program that provides for example, screening airline passengers or patrolling
a 360-degree look at each passenger boarding a flight borders. Response activities occur immediately after
and develops a threat score for use in deciding about a disaster and include stabilizing affected areas,
additional security screening. immediate medical care, and evacuation. Finally,
Pate-Cornell (2002) studied the fusion of intelli- recovery focuses on returning the affected areas and
gence information from different sources and used populations to their pre-event status and includes
Bayesian analysis to rank threats and to prioritize restoring critical infrastructures, assisting affected
safety measures. Dombroski and Carley (2002) used persons, and coordinating relief efforts.
Bayesian analysis and biased network theory to esti- Despite the attention paid to component support,
mate patterns of links between different cells of many critical issues remain to be addressed within
a terrorist organization to predict the structure of this category. Green and Kolesar (2004) described
the terrorist network. Other researchers who devel- how component support problems are evolving. They
oped Bayesian methods to aid in decision making suggested that analysts need to work on nonrou-
are Santos (1996), Santos and Young (1999), and tine emergencies and coordinating emergency service
Santos et al. (2003). Santos and Haimes (2004) used providers, and preparing for and responding to ter-
input-output and decomposition analysis to provide a roristic acts.
framework for describing how various terrorist activ- A wealth of literature concerns the security of
ities are connected. They prioritize sectors based on trucks transporting hazardous materials, largely such
the economic impact of terrorist activities. Haimes issues as routing them to avoid exposing populationsWright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
Interfaces 36(6), pp. 514–529, © 2006 INFORMS 523
Category Planning Prevention Response Recovery
Countermeasures portfolios
Biological Hupert et al. (2002) Sullivan and Perry (2004) Buckeridge et al. (2005), Craft
et al. (2005), Kaplan et al.
(2002, 2003), Stuart and
Wilkening (2005), Wein et al.
(2003)
Chemical Jenkins (2000)
Radiological and nuclear Butler et al. (2005), Dyer et al.
(1998), Munera et al. (1997)
High explosives
Component support portfolios
Border and transportation
security
Border security Wein and Baveja (2005)
Airline security Barnett et al. (2001), Candalino et al. (2004), Barnett (2004), Gilliam (1979),
Leone and Liu (2003), Virta et al. (2003) Jacobson et al. (2000, 2001,
2003, 2005), Kobza and Jacobson
(1996, 1997)
Port and rail Glickman and Rosenfield (1984), Harrald
et al. (2004), Lewis et al. (2003)
Truck Batta and Chiu (1986, 1988),
Berman et al. (2000), Beroggi and
Wallace (1994, 2005), Erkut and
Ingolfsson (2000, 2005), Erkut
and Verter (1998), Giannikos
(1998), Gopalan et al. (1990), Jin
et al. (1996), Kara et al. (2003),
Karkazis and Boffey (1995),
Lindner-Dutton et al. (1991), List
and Turnquist (1998), Raj and
Pritchard (2000), van Steen
(1987), Zografos and
Androutsopoulos (2004)
Critical infrastructure Apostolakis and Lemon (2005), Brown et al. Baskerville and Portougal (2003) Zografos et al. (1998)
protection (2004), Salmeron et al. (2004)
Cyber security Krings and Azadmanesh (2005) Chowdhury et al. (1999), Muralidhar Abouzakhar and Manson (2002),
et al. (1999) Chen et al. (2005), Shindo
et al. (2000)
Emergency preparedness
and response
Early work Carter and Ignall (1970), Carter and Rolph Carter et al. (1972), Ignall et al.
(1974), Chaiken and Dormont (1978a, b), (1982), Swersey (1982)
Chelst (1988, 1990), Green (1984),
Green and Kolesar (1989), Kolesar
et al. (1975), Ignall et al. (1975), Kolesar
and Blum (1973), Kolesar and Walker
(1974), Larson (1972), Rider (1976),
Walker (1974)
Table continues next page
Table 2: Homeland security literature classified along two dimensions reveals opportunities for future research.
We show where each paper fits within the Department of Homeland Security’s research framework and its position
within the disaster life cycle. The two-dimensional framework in this table illustrates where the bulk of OR
models and applications in homeland security exist. This table also highlights important gaps for future research.
Focusing first on the rows in the table, we see that the topics that have received the most attention fall under
the component support portfolios. Emergency preparedness and response contains significant amounts of work,
with emphasis on emergency services location and resource allocation. Other highly important issues that have
seen significant attention are evacuation models and disaster planning and response.Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
524 Interfaces 36(6), pp. 514–529, © 2006 INFORMS
Category Planning Prevention Response Recovery
Location and resource Akella et al. (2005), Ball and Lin (1993), Batta
allocation and Mannur (1990), Batta et al. (1989),
Belardo et al. (1984b), Benveniste (1985),
Berman et al. (1987), Berman and
Larson (1982), Bianchi and Church
(1988), Brandeau and Larson (1986),
Carter et al. (1972), Chelst (1981), Chelst
and Barlach (1981), Chelst and Jarvis
(1979), Church and ReVelle (1974),
Current and O’Kelly (1992), Daskin
(1983), Daskin and Stern (1981), Eaton
et al. (1985), Fitzsimmons (1973),
Fitzsimmons and Srikar (1982), Goldberg
and Paz (1991), Hall (1972), Halpern
(1977), Hogan and ReVelle (1986),
Larson (1974, 1975, 2001), Larson and
Rich (1987), Pirkul and Schilling (1988),
Plane and Hendrick (1977), ReVelle and
Hogan (1989), Saccomanno and Allen
(1988), Savas (1969), Schilling et al.
(1979), Swoveland et al. (1973), Tavakoli
and Lightner (2004), Toregas et al. (1971),
Walker (1974)
Evacuation models Bakuli and Smith (1991, 1996), de Silva and Chalmet et al. (1982)
Eglese (2000), Helbing et al. (2005), Jha
et al. (2004), Mould (2001), Pidd et al.
(1996), Sheffi et al. (1982), Smith (1991),
Smith and Towsley (1981), Southworth
and Chin (1987), Stern and Sinuany-Stern
(1989), Talebi and Smith (1985)
Disaster planning and Barbarosoglu and Arda (2004), Doheny and Averett (2005), Belardo et al.
response Fraser (1996), Haghani and Oh (1996), (1984a), Srinivasa and
Kananen et al. (1990), Miller-Hooks and Wilhelm (1997), Wilhelm and
Mahmassani (1998), Reer (1994) Srinivasa (1997)
Threat analysis Dombroski and Carley (2002), Haimes and Sheth et al. (2005), Wang et al. Santos (1996), Santos and
Horowitz (2004), Kaplan et al. (2005), (2004) Young (1999), Santos et al.
Pate-Cornell (2002), Popp et al. (2004), (2003)
Raghu et al. (2005), Santos and Haimes
(2004)
Table 2: Continued.
unnecessarily and analyzing risks. Researchers should researchers and physical scientists, similar to that of
extend these models to incorporate homeland security Craft et al. (2005). OR methods are well suited for
issues, for example, protecting trucks against terrorist problems pertaining to cyber security, critical infras-
hijacking. tructure protection, threat analysis, and border secu-
Much of the extensive research on airline security rity; however, work in these areas so far is limited
has limited applicability because of changes in secu- (Table 2).
rity systems and policies. Operations researchers have We classified papers in the disaster life cycle based
many new opportunities to contribute in this area. on their main focus (Table 2). The literature has gaps
The countermeasures and component support port- with respect to some phases in the disaster life cycle.
folios offer many other opportunities for contribution. Most OR research in homeland security concerns plan-
The literature on the countermeasures portfolio is in- ning. Some concerns prevention, but we uncovered no
creasing, but many issues still need exploration. Some papers on the recovery phase and very few on the
would benefit from collaboration between operations response phase. There is a need for more research onWright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
Interfaces 36(6), pp. 514–529, © 2006 INFORMS 525
decision making after the disaster. As the 2005 hur- Proceedings of the National Academy of Sciences Web
ricanes made clear, we need to respond effectively site. Despite such possible restrictions, operations re-
to large-scale disasters. Operations research modeling searchers have many opportunities to contribute to
incorporating the complex interconnections between homeland security.
relief agencies and government entities can clarify
these chaotic situations and help relief agencies to
coordinate their efforts. Operations researchers have References
Abouzakhar, N. S., G. A. Manson. 2002. An intelligent approach to
not developed models that support real-time decision prevent distributed systems attacks. Inform. Management Com-
making, such as those proposed by Tien (2003, 2005) put. Security 10(5) 203–209.
in the decision informatics area. In addition, opera- Akella, M. R., R. Batta, E. M. Delmelle, P. A. Rogerson, A. Blatt,
tions researchers should extend to disaster response G. Wilson. 2005. Base station location and channel allocation
in a cellular network with emergency coverage requirements.
such collaborative decision-making frameworks as Eur. J. Oper. Res. 164(2) 301–323.
Raghu et al. (2005). Apostolakis, G. E., D. M. Lemon. 2005. A screening methodology
Research has begun on supply chain security, an for the identification and ranking of infrastructure vulnerabil-
ities due to terrorism. Risk Anal. 25(2) 361–376.
important topic for many corporations. Chopra and
Asbjornslett, B. E., M. Rausand. 1999. Assess the vulnerability of
Sodhi (2004) categorized supply chain risk and risk- your production system. Production Planning and Control 10(3)
mitigation strategies. Russell and Saldanha (2003) 219–229.
discussed increased costs and the changes needed Averett, S. 2005. Building a better bulwark. Indust. Engrg. 37(2)
24–29.
in operating supply chains as a result of terrorist
Bakuli, D. L., J. M. Smith. 1991. Optimal routing and resource allo-
threats. Asbjornslett and Rausand (1999) described cation within state dependent evacuation networks. D. Sulli-
how to reduce the vulnerability of production sys- van, A. B. Clymer, eds. Simulation in Emergency Management
and Engineering. SCS Multiconference, Arlington, 23–30.
tems. Another important issue in need of OR work
Bakuli, D. L., J. M. Smith. 1996. Resource allocation in state-depen-
is private sector response to disasters. For example, dent emergency evacuation networks. Eur. J. Oper. Res. 89(3)
Larson (2006) discussed the need for corporations, 543–555.
such as commercial airlines and manufacturers, to Ball, M. O., F. L. Lin. 1993. Reliability model applied to emergency
service vehicle location. Oper. Res. 41(1) 18–36.
resume normal operations quickly after a disaster.
Barbarosoglu, G., Y. Arda. 2004. A two-stage stochastic program-
The failures of critical infrastructures subjected to ming framework for transportation planning in disaster re-
hurricanes and other natural disasters highlight the sponse. J. Oper. Res. Soc. 55 43–53.
need for research exploring the interdependence of Barnett, A. 2004. CAPS II: The foundation of aviation security. Risk
Anal. 24(4) 909–916.
critical infrastructures and for OR models to predict
Barnett, A., R. Shumsky, M. Hansen, A. Odoni, G. Gosling. 2001.
the likelihood of subsequent failures. Most models Safe at home? An experiment in domestic airline security. Oper.
assume that infrastructures operate in isolation. We Res. 49(2) 181–195.
need to understand the relationships among infras- Baskerville, R. L., V. Portougal. 2003. A possibility theory frame-
work for security evaluation in national infrastructure protec-
tructures to prevent one failure from causing addi- tion. J. Database Management 14(2) 1–13.
tional failures. Batta, R., S. S. Chiu. 1986. Locating 2-medians on tree network with
Research on homeland security can have far-reach- continuous link demands. Ann. Oper. Res. 6 223–253.
ing effects because of its importance to government Batta, R., S. S. Chiu. 1988. Optimal obnoxious paths on a network:
Transportation of hazardous materials. Oper. Res. 36(1) 84–92.
and private agencies. Although these agencies offer
Batta, R., N. R. Mannur. 1990. Covering-location models for emer-
research funding for homeland security research, the gency situations that require multiple response units. Manage-
resulting studies may be classified or published in ment Sci. 36(1) 16–23.
technical reports, and not released for publication in Batta, R., J. Dolan, N. Krishnamurthy. 1989. The maximal expected
covering location problem: Revisited. Transportation Sci. 23
traditional academic outlets. The funding agencies 277–287.
may also see the details of the work as beneficial to Belardo, S., K. R. Karwan, W. A. Wallace. 1984a. Managing the
terrorist groups. For instance, in a Washington Post response to disasters using microcomputers. Interfaces 14(2)
29–39.
article, Weiss (2005) reported that a paper concern-
Belardo, S., J. Harrald, W. A. Wallace, J. Ward. 1984b. A partial cov-
ing the security of the US milk supply by Lawrence ering approach to siting response resources for major maritime
M. Wein and Yifan Liu was removed from the oil spills. Management Sci. 30(10) 1184–1196.Wright, Liberatore, and Nydick: Survey of Operations Research Models and Applications in Homeland Security
526 Interfaces 36(6), pp. 514–529, © 2006 INFORMS
Benveniste, R. 1985. Solving the combined zoning and location Chalmet, L. G., R. L. Francis, P. B. Saunders. 1982. Network models
problem for several emergency units. J. Oper. Res. Soc. 36(5) for building evacuation. Management Sci. 28(1) 86–105.
433–450. Chelst, K. 1981. Deployment of one- vs. two-officer patrol units: A
Berman, O., R. C. Larson. 1982. Median problem with congestion. comparison of travel times. Management Sci. 27(2) 213–230.
Comput. Oper. Res. 9(2) 119–126. Chelst, K. 1988. A public safety merger in Grosse Pointe Park,
Berman, O., Z. Drezner, G. O. Wesolowsky. 2000. Routing and loca- Michigan—A short and sweet study. Interfaces 18(4) 1–11.
tion on a network with hazardous threats. J. Oper. Res. Soc. Chelst, K. 1990. Queueing models for police-fire merger analysis.
51(9) 1093–1099. Queueing Systems 7 101–124.
Berman, O., R. Larson, C. Parkan. 1987. The stochastic queue Chelst, K., Z. Barlach. 1981. Multiple unit dispatches in emergency
p-median problem. Transportation Sci. 21 207–216. services: Models to estimate system performance. Management
Beroggi, G. E. G., W. A. Wallace. 1994. Prototype decision support Sci. 27(12) 1390–1409.
system in hypermedia for operational control of hazardous Chelst, K., J. P. Jarvis. 1979. Estimating the probability distribution
material shipments. Decision Support Systems 12(1) 1–12. of travel times for urban emergency service systems. Oper. Res.
Beroggi, G. E. G., W. A. Wallace. 2005. Operational control of the 27(1) 199–204.
transportation of hazardous materials: An assessment of alter- Chen, W., S. Hsu, H. Shen. 2005. Application of SVM and ANN for
native decision models. Management Sci. 41(12) 1962–1977. intrusion detection. Comput. Oper. Res. 32(10) 2617–2634.
Bianchi, G., R. L. Church. 1988. A hybrid fleet model for emergency Chopra, S., M. S. Sodhi. 2004. Managing risk to avoid supply chain
medical design. Soc. Sci. Medicine 26 163–171. breakdown. MIT Sloan Management Rev. 46(1) 53–61.
Bonder, S. 2002. Army operations research—Historical perspectives Chowdhury, S. D., G. T. Duncan, R. Krishnan, S. F. Roehrig,
and lessons learned. Oper. Res. 50(1) 25–34. S. Mukherjee. 1999. Disclosure detection in multivariate cate-
Brandeau, M., R. Larson. 1986. Extending and applying the hyper- gorical databases: Auditing confidentiality protection through
cube queueing model to deploy ambulances in Boston. TIMS two new matrix operators. Management Sci. 45(12) 1710–1723.
Studies in the Management Sciences 22. TIMS, Providence, RI, Chung, C. 1986. Recent applications of the maximal covering loca-
121–153. tion planning model. J. Oper. Res. Soc. 37(8) 735–746.
Branscomb, L. M., R. D. Klausner. 2003. Making the nation safer: Church, R., J. Current, J. Storbeck. 1991. A bicriterion maximal cov-
The role of science and technology in countering terrorism. ering formulation which considers the satisfaction of uncov-
Committee on science and technology for countering terror- ered demand. Decision Sci. 22 38–52.
ism. The National Academies Press, National Research Coun- Church, R. L., C. ReVelle. 1974. The maximal covering location
cil, Washington, D.C. problem. Papers Regional Sci. 32 101–118.
Brown, T., W. Beyeler, D. Barton. 2004. Assessing infrastructure Craft, D. L., L. M. Wein, A. H. Wilkins. 2005. Analyzing bioterror
interdependencies: The challenge of risk analysis for com- response logistics: The case of anthrax. Management Sci. 51(5)
plex adaptive systems. Internat. J. Critical Infrastructures 1(1) 679–694.
108–117. Current, J., M. O’Kelly. 1992. Locating emergency warning sirens.
Buckeridge, D. L., H. Burkom, M. Campbell, W. R. Hogan, A. W. Decision Sci. 23(1) 221–234.
Moore. 2005. Algorithms for rapid outbreak detection: A Daskin, M. S. 1983. Maximum expected covering location model:
research synthesis. J. Biomedical Informatics 38(2) 99–113. Formulation, properties and heuristic solution. Transportation
Butler, J. C., A. N. Chebeskov, J. S. Dyer, T. A. Edmunds, J. Jia, V. I. Sci. 17(1) 48–70.
Oussanov. 2005. The United States and Russia evaluate plu- Daskin, M. S., E. N. Stern. 1981. A hierarchical objective set cover-
tonium disposition options with multiattribute utility theory. ing model for emergency medical service deployment. Trans-
Interfaces 35(1) 88–101. portation Sci. 15(2) 137–152.
Candalino, T. J., S. H. Jacobson, J. E. Kobza. 2004. Designing optimal Department of Homeland Security. 2005. Retrieved July 1, 2005. http://
aviation baggage screening strategies using simulated anneal- www.dhs.gov/dhspublic/interapp/editorial/editorial_0413.xml.
ing. Comput. Oper. Res. 31(10) 1753–1767.
de Silva, F. N., R. W. Eglese. 2000. Integrating simulation model-
Carter, G. M., E. J. Ignall. 1970. Simulation model of fire department ing and GIS: Spatial decision support systems for evacuation
operations. Design and preliminary results. IEEE Trans. Systems planning. J. Oper. Res. Soc. 51(4) 423–430.
Sci. Cybernetics SSC-6(4) 282–293.
Doheny, J. G., J. L. Fraser. 1996. MOBEDIC—A decision modeling
Carter, G., J. Rolph. 1974. Empirical Bayes methods applied to esti- tool for emergency situations. Expert Systems Appl. 10(1) 17–27.
mating fire alarm probabilities. J. Amer. Statist. Assoc. 69(348)
Dombroski, M. J., K. M. Carley. 2002. NETEST: Estimating a terror-
880–885.
ist network’s structure—Graduate student best paper award,
Carter, G. M., J. M. Chaiken, E. Ignall. 1972. Response areas for two CASOS 2002 Conference. Comput. Math. Organ. Theory 8(3)
emergency units. Oper. Res. 20(3) 571–594. 235–241.
Chaiken, J. M. 1978. Transfer of emergency service deployment Dyer, J. S., T. Edmunds, J. C. Butler, J. Jia. 1998. A multiattribute
models to operating agencies. Management Sci. 24(7) 719–731. utility analysis of alternatives for the disposition of surplus
Chaiken, J. M., P. Dormont. 1978a. A patrol car allocation model: weapons-grade plutonium. Oper. Res. 46(6) 749–762.
Background. Management Sci. 24(12) 1280–1290. Eaton, D. J., M. S. Daskin, D. Simmons, B. Bulloch, G. Jansma. 1985.
Chaiken, J. M., P. Dormont. 1978b. A patrol car allocation model: Determining emergency medical service vehicle deployment in
Capabilities and algorithms. Management Sci. 24(12) 1291–1300. Austin, Texas. Interfaces 15(1) 96–108.
Chaiken, J. M., R. C. Larson. 1972. Methods for allocating urban Erkut, E., A. Ingolfsson. 2000. Catastrophe avoidance models for
emergency units: A survey. Management Sci. 19(4, Part 2) hazardous materials route planning. Transportation Sci. 34(2)
110–130. 165–179.You can also read